Published on Thursday 26th March 2026
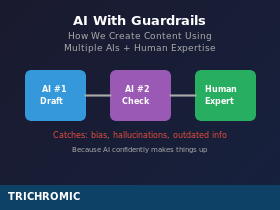
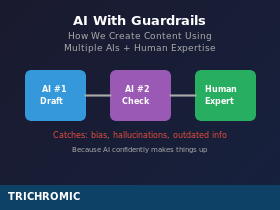
We use AI to help write our news articles and technical guides. We also don’t trust it. Here’s how we combine multiple AI tools with human expertise to create content that’s actually accurate.
You might have noticed we publish quite a lot of articles on technical topics—Windows updates, security threats, regulatory changes, industry news. What you might not know is that we use AI tools to help create them.
We’re not hiding this. We think it’s worth explaining, because the way we use AI is probably different from what you might assume. We don’t just ask an AI to write an article and publish whatever it produces. That would be a disaster. Instead, we’ve developed a workflow that treats AI as a powerful tool that requires constant supervision—like a very fast, very knowledgeable assistant who occasionally makes things up with complete confidence.
Here’s how it actually works, including the mistakes we’ve caught along the way.
The Basic Workflow
Our content creation process typically involves three parties: a human with domain expertise (that’s us), a primary AI for drafting (usually Claude), and a second AI for fact-checking (usually ChatGPT). The human stays involved throughout.
It works like this: Continue reading →
Published on Thursday 26th March 2026
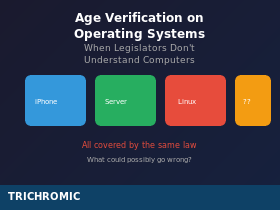
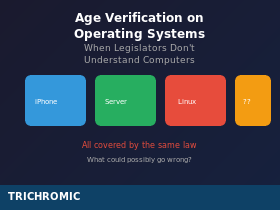
New US laws require operating systems to verify users’ ages. The problem? The people who wrote them appear to think ‘operating system’ means ‘iPhone’. Here’s what UK businesses need to know.
Something rather strange is happening in American technology legislation, and while it might seem like a distant problem, the ripple effects could reach UK businesses sooner than you’d think.
Several US states have passed or are passing laws that require operating system providers to collect age information from users when they set up an account. The intention is to protect children online by making age verification happen at the operating system level, rather than leaving it to individual apps and websites.
The intention is reasonable. The execution is a masterclass in what happens when laws are written by people who don’t understand the technology they’re trying to regulate.
What These Laws Actually Require
California’s Digital Age Assurance Act (AB 1043), signed into law on 13 October 2025 and taking effect on 1 January 2027, is the flagship example. It requires every “operating system provider” in California to collect age information from users during account setup—specifically, their birth date, age, or both—and make that information available to app developers via a real-time API. Continue reading →
Published on Wednesday 25th March 2026
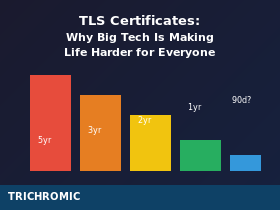
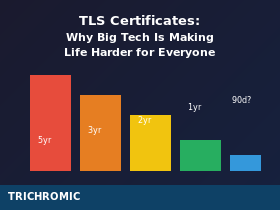
Certificate validity periods have shrunk from five years to one year—and they’re about to get even shorter. Here’s why it’s happening, who benefits, and why small IT teams are paying the price.
This week I renewed a TLS certificate for a client’s booking website. The old certificate was due to expire on 26th March. The new one, freshly issued, expires on 9th October. Not 26th March next year—9th October this year. A one-year certificate that doesn’t actually last a year from when you install it.
This is an Organisation Validated (OV) certificate for a site that takes payments. It required email verification, phone callbacks, and identity checks against official company records. And I’ll be doing it all again in about six months.
It wasn’t always like this. Not long ago, I was renewing these certificates every three years. Before that, every five years. Now it’s effectively twice a year, and if the browser vendors get their way, it could soon be four times a year.
This isn’t a technical improvement. It’s a burden being imposed on the entire industry by a handful of enormous companies who have the infrastructure to automate their way around it—and apparently no understanding of how the rest of us work.
How We Got Here
TLS certificate validity periods are set by the CA/Browser Forum, a consortium that includes certificate authorities (the companies that issue certificates) and browser vendors (the companies that decide which certificates to trust). In practice, the browser vendors hold all the power—if Google or Apple decide not to trust certificates longer than a certain validity, certificate authorities have no choice but to comply. Continue reading →
Published on Wednesday 25th March 2026
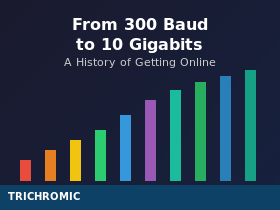
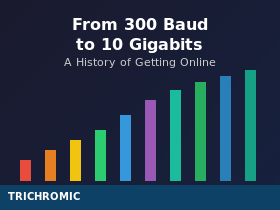
From 300 Baud to 10 Gigabits: A History of Getting Online
Six decades of connection speeds, from acoustic couplers to fibre optics—and why your grandchildren won’t believe how we used to live.
If you’re old enough to remember the sound of a dial-up modem negotiating a connection, you’ll know that getting online used to require patience. Lots of patience. But even if your first experience of the internet was over broadband, the journey from the earliest data connections to today’s gigabit fibre is a remarkable story of engineering progress.
Let’s take a trip through the decades and see just how far we’ve come.
The Beginning: Acoustic Couplers and 300 Baud (1960s–1970s)
Before the internet existed, there were modems. The word itself is a contraction of “modulator-demodulator”—a device that converts digital signals into analogue sounds that can travel over telephone lines, and vice versa. Continue reading →
Published on Wednesday 25th March 2026

Why concentration, supply chains, and geopolitics should factor into your cloud decisions
Most businesses now rely on cloud services for core operations. Email, file storage, line-of-business applications, backups, collaboration tools, and remote access often sit on infrastructure owned and operated by someone else. For many workloads, that makes perfect sense. Cloud services can be flexible, scalable, and cost-effective.
But there is an important conversation that often gets skipped: what are the risks of putting too much of your business into one very large basket?
The concentration problem
When people talk about “the cloud”, they are usually talking about a surprisingly small number of providers. In practice, a huge proportion of business systems ultimately sit on infrastructure operated by Amazon Web Services, Microsoft Azure, or Google Cloud. Continue reading →
Published on Tuesday 24th March 2026

The Trivy breach shows why infrastructure design and operational control still matter
What just happened
In March 2026, security teams disclosed a supply-chain compromise involving Trivy, the widely used open source security scanner. Attackers used compromised credentials to publish malicious Trivy artifacts and tamper with related release channels, turning a trusted security tool into a mechanism for stealing secrets from downstream environments. Public reporting later indicated that more than 1,000 SaaS environments were already dealing with the fallout, with investigators warning that the total could rise significantly.
The incident did not stop with Trivy. As the investigation developed, other projects were linked to the wider campaign, including LiteLLM, where malicious PyPI packages were published and later removed. In LiteLLM’s case, the project’s own incident update said the affected versions were limited to specific package releases, while official Docker-based deployments and source installs were not affected.
The bigger lesson is not just that one tool was compromised. It is that modern environments often depend on long chains of upstream software, build systems, package registries, automation, and release pipelines. When one trusted component is poisoned, the impact can spread quickly into customer environments that never realised they were exposed.
The supply-chain problem
Continue reading →
Published on Tuesday 24th March 2026
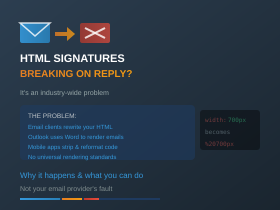
An Industry-Wide Problem With No Perfect Solution
If you’ve ever carefully designed an HTML email signature—complete with logos, formatted text, and proper spacing—only to see it fall apart when someone replies to your email, you’re not alone. This is one of the most frustrating and persistent problems in business email, and it affects virtually everyone who uses custom HTML signatures.
The bad news: there’s no complete fix. The good news: understanding why it happens can help you design signatures that degrade more gracefully, and set realistic expectations for what’s achievable.
What’s Actually Happening
When you send an email with an HTML signature, it looks perfect. But the moment the recipient hits Reply or Forward, their email client rewrites your carefully crafted HTML code to match its own internal standards. Continue reading →
Published on Saturday 14th March 2026
The Economics Behind the Software That Runs the World
Linux powers most of the internet. It runs the majority of web servers, the cloud infrastructure of Amazon, Google, and Microsoft, most smartphones (via Android), supercomputers, and an enormous amount of the world’s critical infrastructure. It’s also, fundamentally, free.
This raises an obvious question: how does any of this get paid for? Who funds the development of software that trillion-dollar companies depend on but don’t have to pay for?
The answer is complicated, and—depending on your perspective—either inspiring or deeply troubling.
Where It All Started
None of this would exist without Richard Stallman. In 1983, Stallman—then a programmer at MIT’s AI Lab—announced the GNU project, an ambitious attempt to create a completely free operating system. In 1985, he founded the Free Software Foundation to support it. Continue reading →
Published on Tuesday 10th March 2026

When Power Settings Aren’t Enough: The Modern Standby Problem
Summary: You’ve configured Windows power settings to prevent your PC from sleeping, but it keeps sleeping anyway. The culprit is likely Modern Standby (also called Connected Standby or S0 Low Power Idle)—a feature on newer hardware that completely bypasses traditional power settings.
The Problem
You’ve done everything right. You’ve gone into Power Options and set the PC to never sleep. You’ve run powercfg commands to disable sleep and hibernate. Maybe you’ve even deployed a script via Intune or Group Policy to enforce these settings across your organisation. Continue reading →
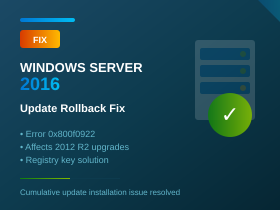
Published on Tuesday 3rd March 2026
Registry Fix for Error 0x800f0922 and Update Rollback Issues
Summary: If your Windows Server 2016 cumulative updates are failing to install—reaching 100% then rolling back with error 0x800f0922—this article explains the multiple causes and fixes. The issues are particularly common on servers that were upgraded from Windows Server 2012 R2, and on Remote Desktop Services (RDS) Session Host servers.
The Problem
Since late 2025, many Windows Server 2016 administrators have been experiencing a frustrating issue: cumulative security updates appear to install successfully, reaching 100%, but then roll back during the restart with the message:
“We couldn’t complete the updates. Undoing changes.”
The error code associated with this failure is typically 0x800f0922 (CBS_E_INSTALLERS_FAILED). This has affected multiple cumulative updates including KB5066836, KB5066136, KB5070882, KB5071543, KB5073722, and others. Continue reading →